Why CoreTrac?
- Unified Customer View
With one unified view, you’ll be able to build better relationships, sell more and expand every opportunity.
- Always Personalized, Always On
Deliver the right message at the right time — always.
- Easy Integration
Integrate with your operations to seamlessly unify how you manage client relationships.
- Grow Revenue
The results are tangible, delivering more revenue growth for your organization, more cross-selling opportunities than ever before and more deals closed.

- Action Center
See all your crucial data in one place with CoreTrac's Action Center, a comprehensive collection of dynamic data views that can be configured to your needs.
- Powerful Reporting
Visualize your data with easy-to-digest reporting. Track sales opportunities, view pipelines and manage employee performance.
- Helpful Snapshots
On customer records, Snapshot pops up to show you a collection of relevant data drawn from several sources within CoreTrac, including cases, cross-sell opportunities and marketing campaigns.
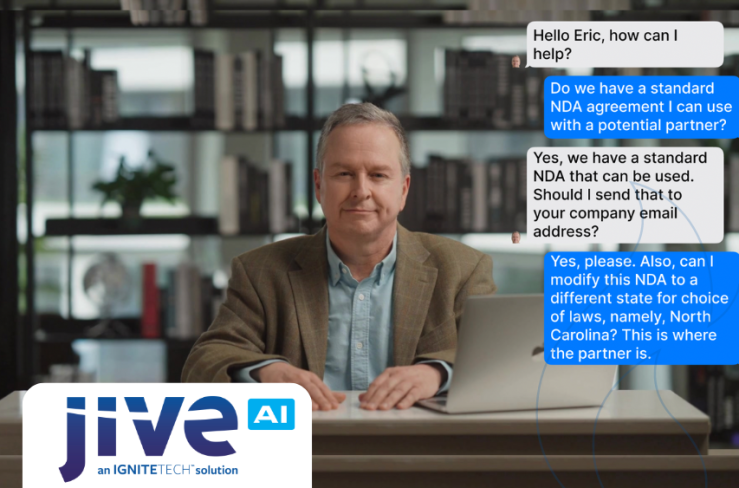
NEW GENAI COPILOT FEATURE
Coretrac CoPilot is a GenAI personal assistant that automates report analysis. It quickly synthesizes complex data on branch performance, referrals, and pipelines, delivering concise, actionable summaries. By delivering rapid insights for strategic planning, CoPilot streamlines decision-making and gives executives more time for other priorities.
BENEFITS
- Time-Saving: Eliminate the hours spent on manual report analysis, freeing up valuable time for other tasks.
- Actionable Insights: Quickly identifies the most critical performance indicators and trends, allowing for data-driven decision-making.
COMPLEMENTARY IGNITETECH UNLIMITED SOLUTIONS
Check out the solutions below, available free as part of your CoreTrac subscription:
AlertFind
AlertFind
Enterprise notifications to communicate important information, monitor responses and verify staff safety.
Blog Posts

Apr 17, 2024
IgniteTech Integrates AI Features Across Its Enterprise Software Portfolio
IgniteTech delivers AI-powered enhancements for 12 of its leading software products, available now…
Apr 11, 2024
Supercharge Your Team: Expert Knowledge on Demand with Jive Personas
Discover how Jive Personas, an innovative AI-driven solution, transforms the way organizations…

Apr 8, 2024
How computers understand Human Language
Unravel the mysteries of how computers understand human language through the fascinating world of…

Mar 28, 2024
IgniteTech Reinvents the Digital Workspace with AI-Powered Jive Personas, Unveiled at ImagineAI Live
IgniteTech CEO Eric Vaughan announces Jive Personas, empowering Jive customers with AI avatars that…

Mar 26, 2024
The Age of Generative AI: A Guide to Exciting New Careers
Generative AI is revolutionizing the way we work, creating new possibilities while raising important…

Mar 5, 2024
Inside IgniteTech's AI-First Transformation: Culture, Products, and Strategy
At IgniteTech, we're boldly transforming our company with an AI-first approach. This blog post…